Washington's Digital Siege: How Sovereign Content-Bypass Portals Threaten the DSA
Six percent of global turnover. That is the maximum penalty the European Union can levy against a digital platform for failing to police content under the Digital Services Act (DSA). For a company like Meta or Alphabet, that figure represents an existential liquidity shock. But for the United States government, the cost to route a packet around those regulations is effectively zero.
We are witnessing a quiet but violent inversion of internet diplomacy. For two decades, Washington funded "circumvention technology" to punch holes in the Great Firewall of China and the RuNet. Now, in a twist of supreme irony, that same stack—funded by the State Department and the Open Technology Fund—is being retooled to dismantle the digital borders of the European Union.
This analysis dissects the emergence of Sovereign Content-Bypass Portals: state-backed infrastructure designed to route around allied content bans. We are moving beyond simple trade disputes into a conflict over the topology of the internet itself, where the U.S. export of First Amendment absolutism is triggering a diplomatic crisis that threatens to fracture the Western web.
Weaponizing Circumvention Tech Against Allied Firewalls
The architecture of the internet is being weaponized to solve a political problem: the divergence of Western values. To understand the threat, one must look at the machinery. The tools currently being deployed are not new; they are repurposed weapons of information warfare.
Repurposing the Open Technology Fund stack
The Open Technology Fund (OTF) was created to support freedom of expression in repressive regimes. Its portfolio includes Tor, Signal, and various obfuscation protocols. However, the definition of "repressive" is becoming fluid in Washington. As the EU tightens its grip on "disinformation" and "hate speech"—categories protected under the U.S. First Amendment—American policymakers are quietly authorizing the use of this stack to bypass European restrictions.
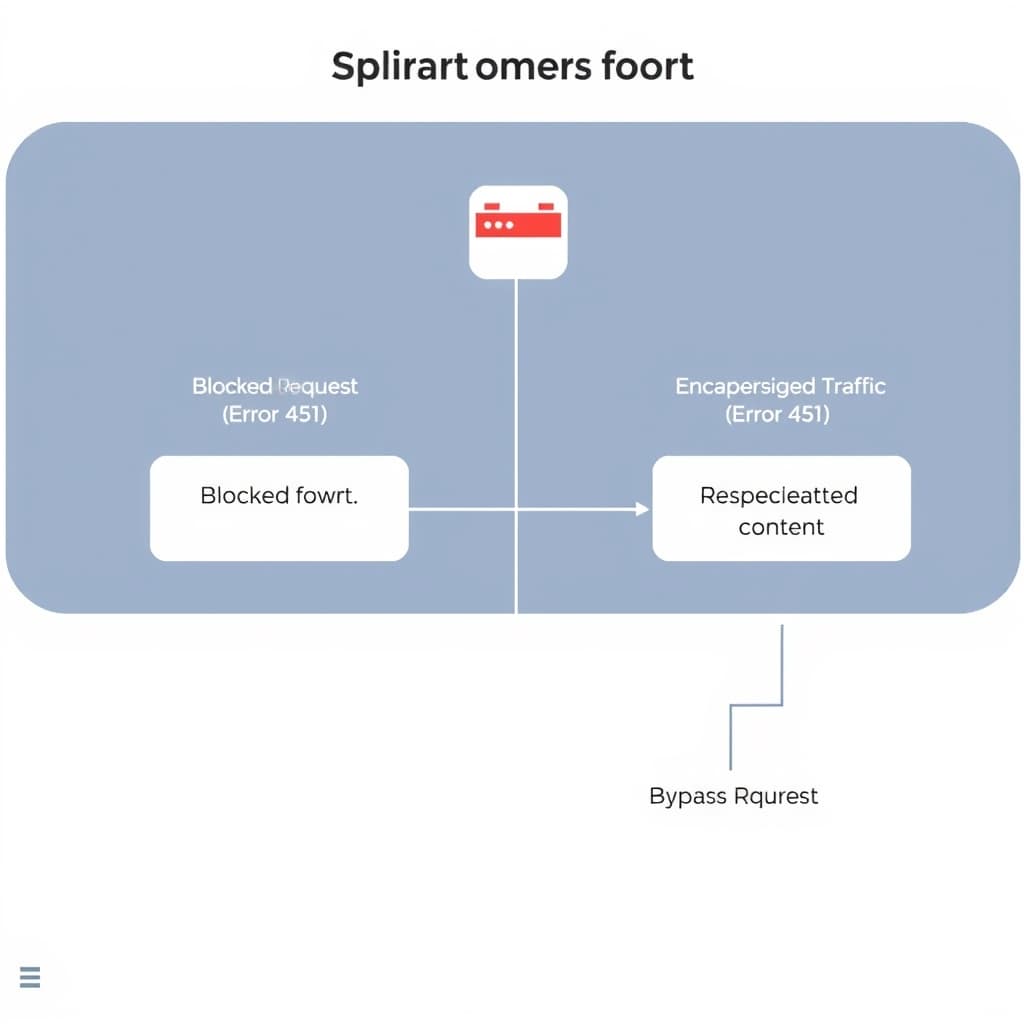
This is regulatory arbitrage via TCP/IP. By encapsulating traffic through sovereign-backed exit nodes, the U.S. creates a "Sovereign Content-Bypass Portal." Unlike a commercial VPN, which can be pressured by local law enforcement, these portals operate under a veneer of diplomatic protection. They are digital embassies; to block the traffic is to blockade the State Department.
From obfuscation to diplomatic routing
Historically, circumvention relied on hiding the nature of the traffic (obfuscation). The new strategy relies on the origin of the traffic. When a user in Berlin accesses a banned narrative via a Sovereign Portal, the request does not appear to come from a private citizen circumventing the DSA. It appears as diplomatic or protected traffic routing through U.S. government-contracted infrastructure. This shifts the burden of enforcement from a technical challenge (blocking an IP) to a geopolitical crisis (blocking a NATO ally's communications).
Case Study: The "Freedom Stack" vs. The Brussels Effect
To visualize the mechanical difference between commercial evasion and sovereign bypass, we must analyze the operational layers. The following comparison highlights why European regulators find the latter impossible to police without escalating to trade war tactics.
The "Shadow IT" of Statecraft
Consider the recent friction regarding platform regulation. When the EU threatens to ban a platform for non-compliance, the U.S. response has historically been diplomatic protest. The new "Freedom Stack" creates a tangible alternative: a federally funded "Shadow IT" infrastructure.
If a platform is blocked in France for refusing to remove content that is legal in the U.S., a Sovereign Portal allows the platform to remain accessible via a "US-Protected Mode." The browser request is encapsulated, routed through a US-controlled entry node, and delivered back to the user. The platform complies with US law, the user accesses the content, and the EU's digital sovereignty is rendered unenforceable.
First Amendment Exports vs. The Brussels Effect
The collision is not merely technical; it is philosophical. The "Brussels Effect"—the EU's ability to unilaterally set global standards through market size—has finally hit the immovable object of American free speech maximalism.
The collision of safety and speech
Washington is waking up to the reality that the DSA is not just a safety framework; it is a containment strategy for American soft power. The "Right to be Forgotten" and strict liability for algorithms are viewed by U.S. free speech advocates as information suppression mechanisms. By deploying bypass portals, the U.S. is effectively saying that its domestic law travels with its packets. If the data resides on a U.S. server, and the routing is U.S.-funded, the First Amendment applies, regardless of where the pixels are displayed.
"Internet Freedom" as a weapon
This reframes "Internet Freedom" from a humanitarian aid concept into a trade weapon. The U.S. argument is shifting: restricting access to American digital platforms via the DSA is a non-tariff trade barrier. Therefore, bypassing those restrictions is not subversion; it is the enforcement of free trade agreements. This logic transforms the DSA from a domestic regulation into a violation of international commerce, justifying the deployment of bypass infrastructure.
Silicon Valley’s Impossible Compliance Dilemma
For the tech giants, this geopolitical chess match is a nightmare scenario. They are caught between the threat of 6% global turnover fines in Europe and the pressure to align with U.S. strategic interests.
Navigating the legal paradox
Platforms are facing a bifurcated reality. In the EU, they must build backdoors for regulators and suppression tools for "harmful" content. In the U.S., they are increasingly pressured to refuse foreign censorship demands. The Sovereign Content-Bypass Portal offers a seductive, dangerous third option: State-Sponsored Non-Compliance.
Companies may soon integrate "Sovereign Routing" directly into their apps. Instead of a user needing a separate VPN, the app itself detects an EU block and automatically reroutes traffic through the U.S. portal. This allows the company to tell EU regulators, "We didn't serve this content; the user fetched it via U.S. government infrastructure." It is a high-stakes game of jurisdictional chicken.
The Inevitable Rise of the NATO Splinternet (2026-2030)
If the U.S. persists in deploying these portals, the reaction from Brussels will be kinetic. We are moving toward a "NATO Splinternet," where allies erect digital borders against each other.
Retaliatory Deep Packet Inspection (DPI)
European ISPs will be forced to implement Deep Packet Inspection (DPI) technologies previously associated with authoritarian regimes. To distinguish between legitimate traffic and "Bypass Portal" traffic, European telecoms will need to inspect the header and payload of packets entering from the U.S. This will slow down trans-Atlantic commerce and raise privacy concerns that dwarf current debates.
The degradation of global DNS
The ultimate casualty will be the Domain Name System (DNS). If the U.S. uses the root zone to enforce its view of openness, the EU will accelerate its push for a sovereign DNS (DNS4EU). This will fracture the root zone. A URL will no longer resolve to the same server in Paris as it does in New York. The universal address book of the internet will tear along the Atlantic fault line.
Prediction: The Systemic Risk Designation
Falsifiable Claim: By Q4 2027, the European Commission will formally designate a U.S. government-funded privacy tool (likely a derivative of the Tor or Psiphon protocol) as a "Systemic Risk" under Article 34 of the Digital Services Act.
Indicators to Watch:
- EC Audits: An increase in EC requests for technical audits of "anonymization services" used by EU citizens.
- Funding Bills: Specific line items in the U.S. State Department budget allocated for "Open Internet access in regulated democratic markets."
- ISP Mandates: New EU directives requiring ISPs to block "unauthorized routing protocols" that obscure jurisdictional origin.
The End of the Interoperable West
The era of a seamless Western internet is concluding. As the U.S. formalizes these bypass portals, European regulators will be forced to treat American digital traffic with the same suspicion previously reserved for hostile state actors. The next trade war won't be over steel or cars, but over the right to route packets through sovereign airspace. When allies begin firewalling each other, the global internet effectively dissolves.
FAQ
How do Sovereign Content-Bypass Portals differ from commercial VPNs? Unlike commercial VPNs, which are private entities subject to local laws and server seizures, these portals operate on state-backed infrastructure with diplomatic immunity, making them virtually impossible for host nations to shut down without triggering a geopolitical incident.
Is this infrastructure a violation of international law? It resides in a legal gray zone. While nations have sovereignty over their telecommunications, the U.S. argues that the free flow of information is a human right that supersedes domestic content restrictions, effectively weaponizing the concept of 'Internet Freedom' against allied regulations.