Digital False Flags: Why Commercial Fleets Are Spoofing Chinese Identities in the Gulf
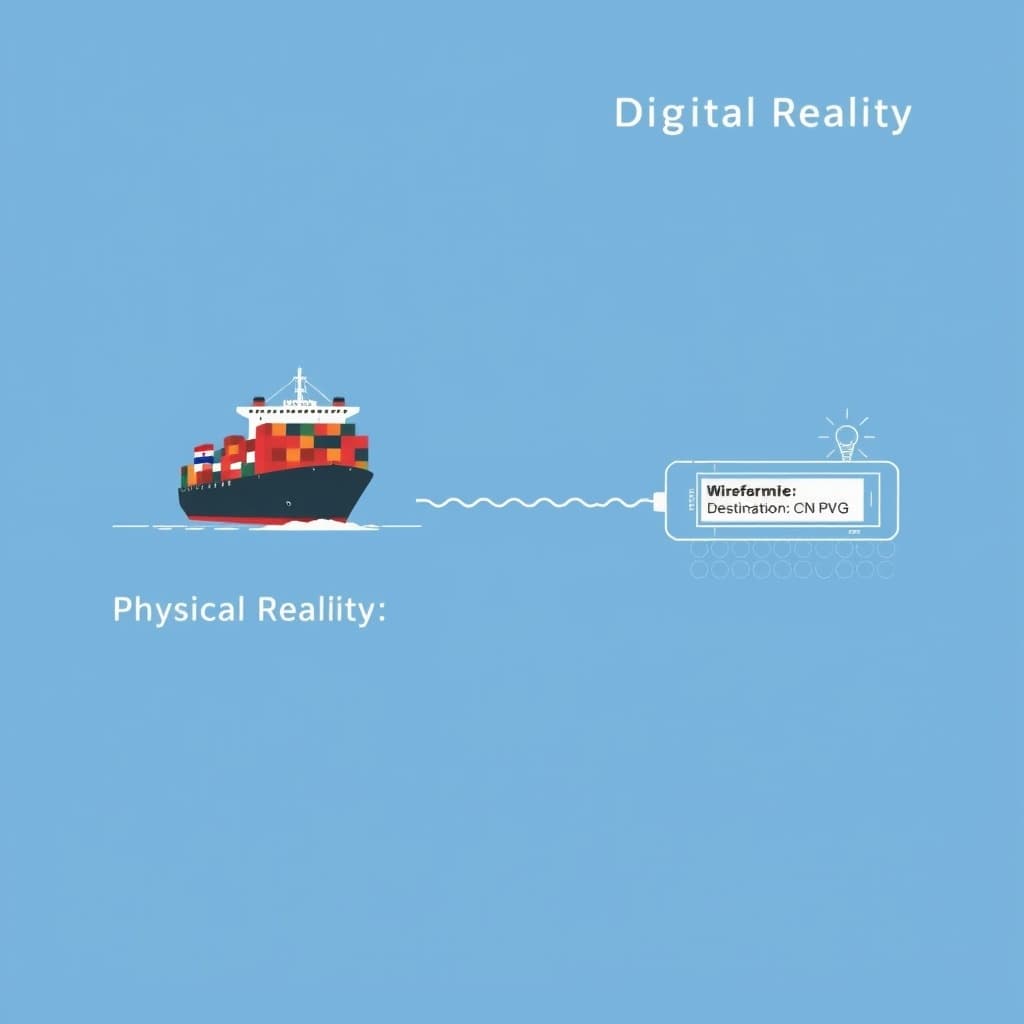
When a Liberian-flagged bulk carrier recently traversed the Bab el-Mandeb Strait, its physical hull displayed standard Western registration markings, but its digital exhaust told a different story. To the electromagnetic spectrum, the vessel was indistinguishable from a distinct asset class: a Chinese-owned logistics freighter destined for Shanghai. This discrepancy is not a glitch; it is Geopolitical Digital Masking, a defensive strategy where commercial operators weaponize identity data to exploit the specific rules of engagement (ROE) programmed into adversarial targeting systems.
This analysis dissects how the maritime sector is shifting from physical armor to information warfare, effectively turning the Automatic Identification System (AIS) into a battlefield shield.
The Mechanics of Identity Theft at Sea: Manipulating AIS Transponders
The backbone of maritime safety—the AIS protocol—was designed for transparency, not security. It operates on open VHF frequencies without native encryption, making it trivially easy to manipulate with Software-Defined Radios (SDR) or even administrative access to onboard bridge systems.
Overriding Static Voyage Data vs. Dynamic GNSS Spoofing
There are two distinct layers to this deception. The most common "soft" spoofing involves crew members manually altering the Static Data fields in the AIS transponder. Captains change the "Destination" field to "ALL CHINESE CREW" or "NO ISRAEL CONTACT"—a semantic plea to human operators monitoring the frequencies.
However, the "hard" spoofing required to fool automated missile systems is far more technical. This involves altering the Maritime Mobile Service Identity (MMSI)—the unique nine-digit code that acts as a ship's digital passport. By reprogramming the transponder to broadcast a 412, 413, or 414 prefix (China’s country codes), a vessel fundamentally changes its electronic nationality. This is not merely lying on a form; it is digital flag-swapping that requires overriding firmware locks or employing external SDR peripherals to broadcast a false signal that overpowers the legitimate transponder.
The Hardware Accessibility of Deception
Ten years ago, spoofing AIS required state-level electronic warfare capabilities. Today, the democratization of SDR hardware means a $300 HackRF One and open-source GitHub repositories allow sophisticated signal injection. Commercial fleets are now retrofitting what are effectively electronic countermeasure (ECM) suites, previously the domain of navies, to emit false telemetry that aligns with the "safe lists" of Houthi and Iranian-backed drone logic.
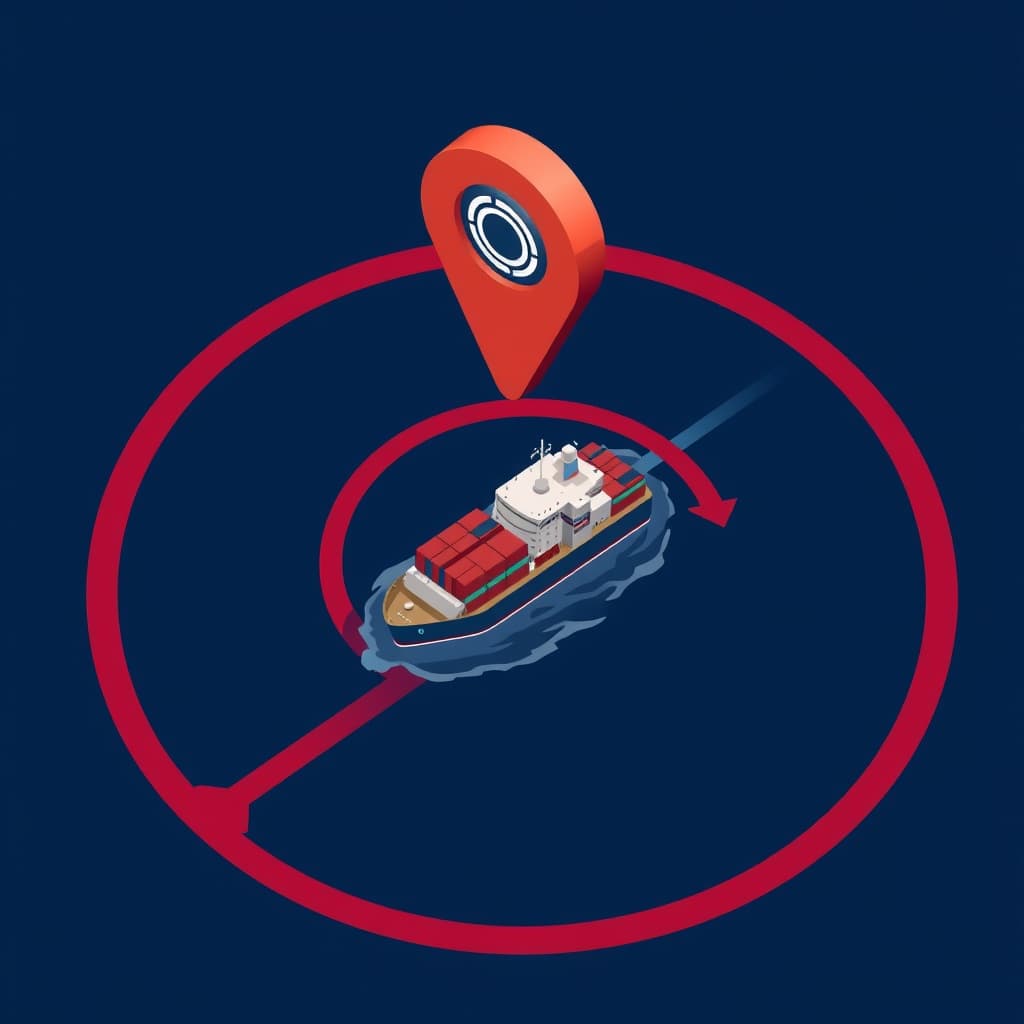
The 'CN' Shield: Exploiting Adversary Rules of Engagement
The effectiveness of spoofing a Chinese identity relies entirely on the geopolitical calibration of the attacker’s algorithms. The "CN" Shield works because non-state actors in the Red Sea and Persian Gulf operate under strict diplomatic constraints regarding Beijing.
Why Chinese Digital Signatures Provide Immunity
China is a primary purchaser of Iranian oil and a critical economic partner for nations bordering the Red Sea. Consequently, the ROE for Houthi drone swarms likely includes "negative targeting" filters—code that specifically aborts engagement if the target’s AIS signature correlates with Chinese registration databases.
By broadcasting a Chinese MMSI, Western vessels are effectively hacking the political logic of the missile. They are betting that the automated kill chain prioritizes diplomatic safety over radar cross-section analysis. Data from maritime AI firms like Windward suggests a statistically significant correlation between vessels broadcasting Chinese affiliation and safe passage rates through high-risk zones, validating the market's rapid adoption of this tactic.
Map of Incentives: The Spoofing Ecosystem
- Commercial Operators (Wins): drastically reduce insurance premiums (War Risk premiums can exceed 1% of hull value per transit) and protect crew lives without expensive private maritime security contractors.
- Insurers (Loses): face a "black box" risk environment. If a ship spoofs its identity and is hit, the policy may be voided due to breach of warranty, yet proving the spoof post-destruction is forensically difficult.
- The Attacker (Mixed): Low-cost drones rely on cheap sensors (AIS/RF). To counter spoofing, they must upgrade to expensive optical or thermal guidance, raising the cost-per-attack.
- China (Loses): As more non-Chinese ships use the "CN" shield, the immunity dilutes. If a "fake Chinese" ship is hit, it causes diplomatic confusion; if a real Chinese ship is hit because the attackers stop trusting the signal, Beijing's strategic leverage erodes.
Collateral Damage: When Algorithmic Targeting Adapts
The widespread adoption of Geopolitical Digital Masking is accelerating a dangerous feedback loop. As the signal-to-noise ratio in AIS data collapses, targeting systems are evolving from reliance on cooperative data (AIS) to non-cooperative recognition.
The Risk of Spoofing Saturation
If a critical mass of vessels identifies as Chinese, the "CN" signal loses its value as a discriminator. This leads to Spoofing Saturation, where attackers disable AIS filtering entirely and revert to "free fire" zones based on radar signatures alone. This endangers legitimate neutral traffic that previously relied on accurate AIS broadcasting for safety.
Evolution Toward Anomaly Detection
Advanced autonomous systems are already moving beyond declared flags. They are beginning to cross-reference AIS data with kinematic behavior. A vessel claiming to be a Chinese fishing trawler (often a convenient cover) but moving at 18 knots on a ballistic trajectory toward the Suez Canal creates a "kinematic dissonance." Future drone swarms will likely target these anomalies—discrepancies between who you say you are and how you move—rather than the flag code itself.
The War for Signal Integrity: Cryptographic Verification and VDES
The maritime industry is approaching a bifurcation point. The current open AIS standard is obsolete for security purposes. The response is the VHF Data Exchange System (VDES), which includes provisions for authentication.
Moving Beyond Open AIS
Regulators and tech providers are pushing for encrypted identity layers where a ship’s MMSI is cryptographically signed. This would function similarly to SSL/TLS on the web—a drone could mathematically verify that the "Chinese" signal originated from a transponder with keys issued by the Chinese maritime authority.
However, this creates a regulatory paradox. The International Maritime Organization (IMO) mandates AIS for safety (collision avoidance), which requires openness. Naval strategy requires opacity. We are heading toward a future where ships carry two digital identities: a clear, unencrypted layer for port authorities and collision avoidance, and an encrypted, authenticated layer for navigating contested waters.
What Would Change My Mind
My assessment of the "CN Shield" viability relies on the assumption that attackers are using low-cost, RF-dependent guidance systems. If Houthi or Iranian proxies rapidly deploy affordable, edge-compute capable drones with onboard optical recognition (visual AI) that can identify ship liveries and stack configurations regardless of AIS output, digital spoofing will become instantly obsolete. Furthermore, if Beijing publicly condemns this practice and shares a real-time "allowlist" of authenticated Chinese MMSIs with regional actors, the spoofing defense will collapse overnight.
Conclusion
Digital masking has turned logistics data into a battlefield shield, forcing a fundamental rethink of how we authenticate assets in international waters. The era of trusting a ship's broadcast data is over. For venture allocators and logistics strategists, the value proposition is shifting from simple tracking software to Signal Integrity Verification—platforms that can distinguish between a vessel's digital claim and its physical reality. Watch for the IMO's upcoming pivot toward encrypted transponder standards, as the current "honor system" of the high seas has been permanently breached.
FAQ
Is modifying AIS data to avoid missile attacks legal under international law? Technically, falsifying AIS data violates IMO SOLAS Chapter V regulations regarding the safety of navigation. However, in active war zones, captains often invoke "force majeure" or self-defense justifications (necessity) to protect the lives of the crew. This creates a complex legal gray zone that insurers and admiralty courts are currently struggling to adjudicate.
Can autonomous drones distinguish between a real and a spoofed digital flag? Most low-cost drones (the type commonly used in asymmetric naval warfare) rely heavily on RF emissions and AIS data streams for initial targeting. Without secondary verification layers like optical recognition or radar signature analysis—which require significantly more expensive hardware and processing power—these systems are highly susceptible to accepting the spoofed data as truth.
Sources
- IMO International Convention for the Safety of Life at Sea (SOLAS), 1974
- International Telecommunication Union (ITU) - Technical Characteristics for AIS
- Windward Maritime AI - Geopolitical Risk Analysis
- U.S. Department of the Treasury - Sanctions Advisory on Deceptive Shipping Practices
- Lloyd's List - Maritime Intelligence
Related
View all →